top of page
SecuSolutions Blog
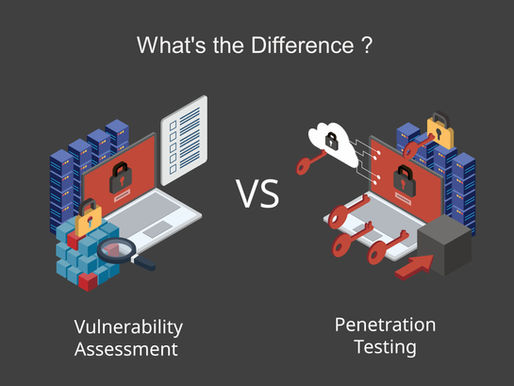
A Vulnerability Assessment is NOT a Penetration Test
A Vulnerability Assessment is NOT a Penetration test. Don’t be misled, it could be a costly mistake. Before starting my first security company in Japan in 1999, a security administration tool called Satan was released. This appears to be the first assessment tool made available to scan networks and identify possible vulnerabilities. Shortly after, the Common Vulnerabilities and Exposures (CVE) data base was made available. Together these platforms paved the way for other comp
jimkootnekoff
3 min read
Don’t Drink the Marketing Cool Aid
Marketing is a masterful art. It works on each and everyone of us in different ways. It could be an advertisement on a car you’ve been dreaming of, or it could be a new gadget you think you may need. It might be a motorcycle or a new RV but whatever it is that got you to buy, clever marketing has played a role in it. You may be thinking, what does this have to do with work or my profession. How does marketing affect me and what’s this got to do with security? It affects you t
jimkootnekoff
3 min read
Introducing your Weakest Security Link
Isn’t it interesting that despite all the statistics that suggest humans are the weakest security link, many organizations turn a blind eye to the importance of providing their staff with information security (InfoSec) awareness security training or the tools to help them defend the corporation they work for? Many of the corporations that SecuSolutions Ltd. serves have nothing in place. No policy, no rules …no guidance. This is alarming since these corporations are of signifi
jimkootnekoff
2 min read
Executive Management and the IT Department, The Great Divide
For the past 24 years (and likely the foreseeable future), executive leadership and the IT Department have seen things differently… a lot differently. This stems mainly from the fact that executive management does not completely understand the needs of the IT department, and the IT department feels the same way about leadership. The concept of cybersecurity is as wide as the Grand Canyon, and cybersecurity may as well be a four-letter word to executive management. They recogn
jimkootnekoff
2 min read
Your IT Guy is NOT your Security Guy
For the last nearly 23 years of running a cybersecurity company, one thing has remained consistent and that is that IT staff, sys admins, network admins, love to hate security personnel. I say this because of the countless times we have been hired by companies to provide a security service only to be met with a line of defence stronger than the Chicago Bears had back in 1985. It is like there are two opposite forces at play within the same organization. Management recognizes
jimkootnekoff
5 min read
The Pandemic – Our Worst Nightmare – A Hackers Dream Come True
There is no doubt that the pandemic has caused great hardships on people, the economy, and a host of other things that we may not feel the impact on for months and or years to come. There is no doubt that the pandemic has caused great hardships on people, the economy, and a host of other things that we may not feel the impact on for months and or years to come. One thing is for certain, all is well in the cybersecurity space. Hackers are busy hacking. Phishers are busy Phishi
jimkootnekoff
4 min read
Cybersecurity & the Digital Supply Chain
Did you know that in the post-COVID world, there is an accelerated and necessary adoption of digital technologies throughout the industrial world in the quest of operational advantage and excellence? The Hackett Group reports that adoption of supply chain network design and optimization tools, are expected to grow from 63% to 81% in the next two years. This means that in Supply Change management and execution, there will be: - increased reliance on automated systems, - re
George Rafael
4 min read
bottom of page

